Collecting people’s information in bulk tend to increase the probability of malicious exploitation and theft.
With the development of technology, the increase numbers of people tend to rely on using digital platform to convenience their life. For example, People communicate with others online, people shopping online, and people order their food online. Therefore, Various number of Digital platforms occur on the society. But most of them require people add their personal information before people use the platform. Some platforms even require tracking people’s location and monitoring their browsing history. Bace on that, Significant numbers of people are worried about if their privacy security will be protected well or not. Hence, the argument of if private businesses should collect, storing, sharing and utilizing data about people had been discussed.

“Facebook growth” by niallkennedy is licensed under CC BY-NC 2.0.
In this essay, I will collect and study a large number of real cases to demonstrate that while collecting people’s information has some benefits, it also increases the probability of malicious exploitation and theft. The purpose of my research in this article is to raise awareness about privacy breaches, making people realize the importance of personal information and appeal people to be careful about uploading private information online.
Collecting data in bulk is more hurt than goods:
There are a few benefits that collecting people’s information by private companies. For example, through the collection of people’s private information and records of their searches, browsing history, or hobbies and interests, individuals are often targeted with recommendations for products by different advertisers when they are contemplating whether to make a purchase. This not only allows advertising companies to operate more efficiently but also provides convenience for their customers who need certain products. However, according to the research collecting people’s information and data is actually more hurt than goods. A significant number of advertisement companies utilize people’s information and data to obtain people’s desires and precisely pushing intrusive advertisements to mislead them and led to a significant burden on people’s lives. For instance, as O’Neil and Cathy point out, predatory advertising has been defined as a weapon of mass destruction. The Internet seems to provide the perfect tool for predatory advertising (2016). Even some for-profit universities have started using data to collect information about poor individuals who aspire to improve their lives and social status. They utilize the desires and needs of these people, gleaned from the data, to precisely deliver intrusive advertisements to deceive them. These predatory advertisements disseminated by for-profit universities often succeed in deceiving impoverished individuals because they promote exactly what these individuals desire. Impoverished individuals aspire to change their circumstances through higher education. However, the reality is that the degrees advertised by these predatory advertisements are far from being as valuable as they are portrayed to be and can even be considered as having little to no value. As O’Neil points out, many of the degrees offered by these universities are not only no more valuable than a high school diploma, but the tuition they charge is often significantly higher than the normal price (2016). Therefore, predatory advertisements lead impoverished students to borrow significant amounts of money in exchange for degrees that lack competitiveness in the job market, creating a massive and vicious cycle of debt for the poor. There are many more examples of such adverse effects caused by data collection. In the Internet fraud casebook: the World Wide Web of deceit. As Wells points out that” The internet is increasingly being used for malicious purposes, and various forms of cyberattacks are becoming more common. Without proper security measures, thieves can even use the internet to steal people’s bank accounts or credit card information.” (Wells,2010). When people’s privacy is collected in bulk, it seems to lead to an increase in crime. These cases seem to lean toward demonstrating the downsides of collecting people’s data being more significant.

“Anonymous computer hacker over abstract digital background. Obscured dark face in mask and hood. Data thief, internet attack, darknet fraud, dangerous viruses and cyber security.” by focusonmore.com is licensed under CC BY 2.0.
The extensive collection of data has resulted in data leaks and illegal exploitation:
Moreover, the disclosure and illegal theft of personal information caused by the collection of people’s data have also become a significant stressor in people’s lives. Various applications and websites collect vast amounts of people’s private information. This not only makes people more susceptible to predatory advertisements but also leads to an increase in fraud resulting from the illegal theft of personal identities. The extensive collection of personal information makes it easier for scammers to steal such information. The Duolingo Data Breach is a good example of this. The breach resulted in the compromised information of more than 2.6 million Duolingo users, including names, email addresses, phone numbers, social media information, and the languages users were studying at the time of the breach (Tech.co, 2023). Information thieves only need to successfully breach one company’s information security system to gain significant profits. Kayla previously pointed out, “Such a situation unfolded when NSO Group, an Israeli hacking tool developer, allegedly built and sold a product that allowed the infiltration of WhatsApp’s servers due to an identified weakness. This problem caused at least 1,400 users to have their mobile phones hacked within approximately two weeks in April and May 2019. A sizeable segment of the identified victims were reportedly high-profile government officials located in at least 20 countries” (2021). Furthermore, according to investigations, “Australians suffered a record $3.1 billion in losses due to scams in 2022,” with scams related to identity theft accounting for a quarter of the total losses in 2022 (ACCC, 2023). The theft of personal and private information has made it increasingly difficult for people to identify scams. Scammers impersonate people’s family members or friends using their information to gain trust. Some fraudsters even use official phone numbers, email addresses, and websites to carry out scams, impersonating legitimate organizations.
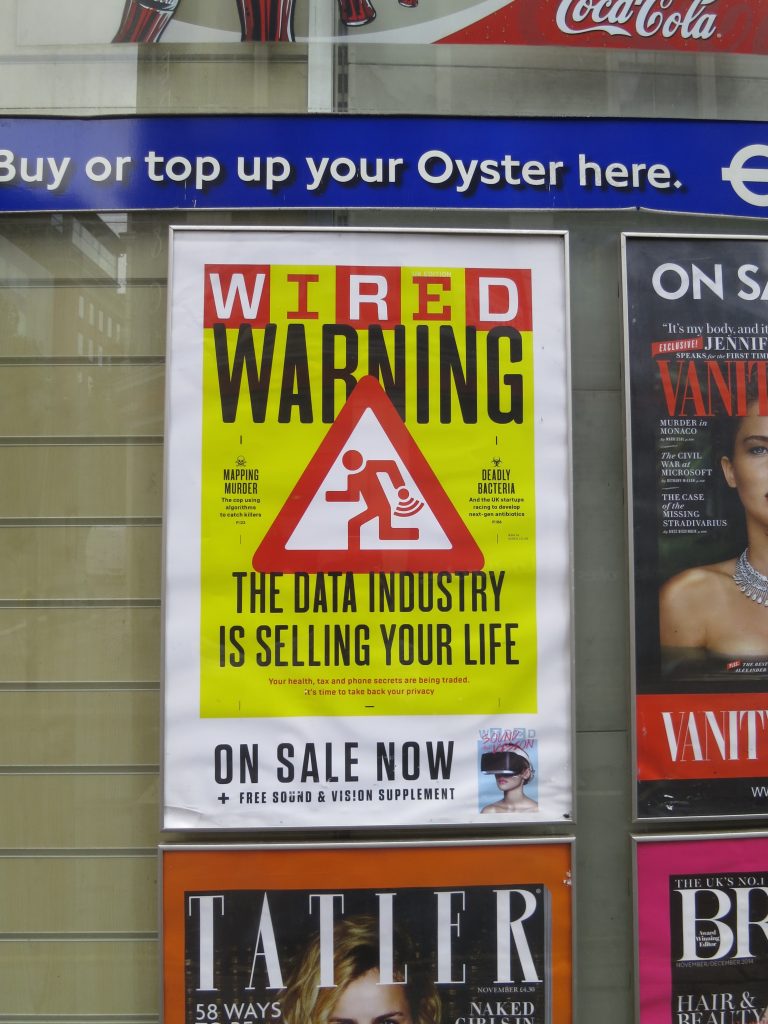
“The Data Industry Is Selling Your Life” by illustir is licensed under CC BY 2.0.
Data is being trafficked without permission:
Furthermore, the extensive collection of personal information has also resulted in a serious infringement of people’s privacy rights. As O’Hara and Hall mention, “China and many other countries have implemented authoritarian internet management approaches, believing that monitoring and identification technologies are beneficial for ensuring social cohesion and security” (2018). China achieves this by encouraging people to use its own tech giants’ programs and websites, such as Baidu, Tencent, and Alibaba. They then exercise strict control and regulation over these large private companies to monitor people on the internet. In 2018, China even compelled Apple to move data related to Chinese users on its iCloud to a data center in China to strengthen control over the internet (O’Hara & Hall, 2018). While this is an effective management approach that ensures social cohesion and security, it also appears to make people’s private information more susceptible to malicious exploitation by private enterprises. Private companies, in pursuit of greater profits, have engaged in the unauthorized sale of people’s information without their consent. For example, Facebook has been accused of secretly selling user data without user consent. Consequently, “the U.S. Federal Trade Commission (FTC) imposed a $5 billion fine on Facebook for its misconduct” (Kayla, 2021).
Based on the above issues, I believe that the value created for customers by private businesses collecting, storing, sharing, and utilizing data about them and others does not outweigh the risks. Allowing private companies to collect vast amounts of people’s information not only leads to the malicious exploitation of that information but also increases the risk of people falling victim to scams. These consequences can have a significant and detrimental impact on people’s lives.
Reference list:
Cybernews. (2021). 6 examples of online privacy violation. https://cybernews.com/privacy/6-examples-of-online-privacy-violation/
Mend.io. (September 21, 2023).Malicious Packages Special Report – Attacks Move Beyond Vulnerabilities. https://youtu.be/CTXr6Lxu3HQ?si=DUJVcJtSQc-MUk4q
O’Hara, & Hall, W. (2018). Four Internets: The Geopolitics of Digital Governance (No.206). Centre for International Governance Innovation. https://www.cigionline.org/publications/four-internets-geopolitics-digital-governance RIDE SHARE GUY. (2023). Uber Driver Review 2023. https://therideshareguy.com/uber-driver-review/
O’Neil, C. (2016). Propaganda machine: Online advertising. In Weapons of math destruction: How big data increases inequality and threatens democracy (pp. 68-83). Crown.).
Tech.co. (2023). Data Breaches That Have Happened in 2022 and 2023 So Far.
https://tech.co/news/data-breaches-updated-list
Wells, J. T. (2010). Internet fraud casebook: the World Wide Web of deceit. John Wiley & Sons.
